When we think about modern cyber threats, USB drives and keys are probably not the first things that come to mind. However, if one attack is successful, other malicious actors will follow along.
And this is why now, on top of AI attacks and elaborate phishing efforts, we are also seeing a renewed interest in attacks using USB drives.
As an example, during Maya Horowitz’s recent keynote presentation at CPX 2024, she shared how USB devices had been recently used by major threat groups to successfully infect sensitive organizations.
According to her keynote, via DarkReading, USBs represented the main infection vector for three different major threat groups in 2023: China’s Camaro Dragon; Russia’s Gamaredon, and the threat actors behind Raspberry Robin.
How a USB Attack Begins
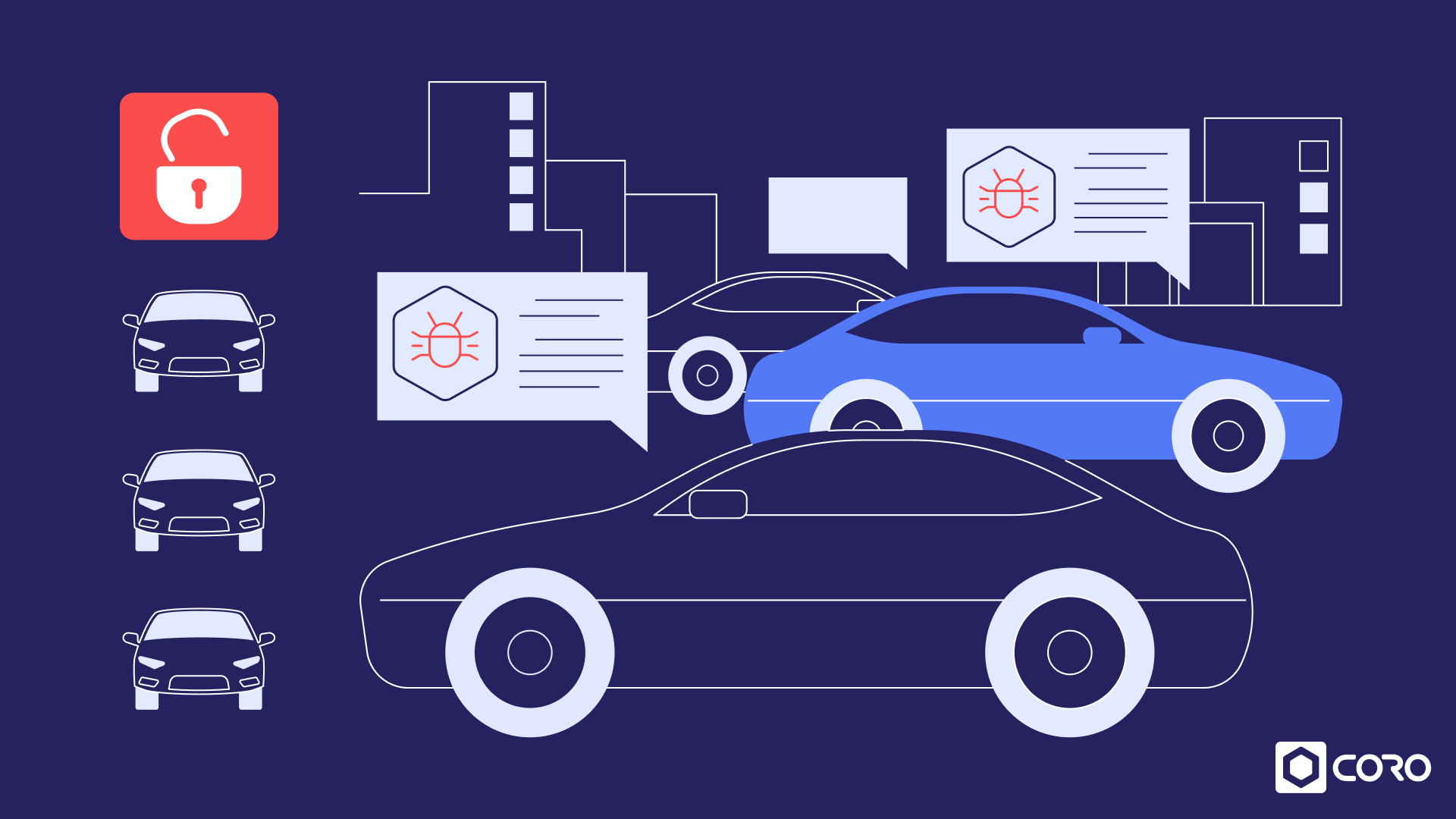
A USB attack involves the use of USB drives or devices to infiltrate systems, steal data, or deploy malicious software.
Despite advancements in technology, humans remain the weakest link in cybersecurity. Some USB attacks exploit human curiosity or negligence by enticing users to insert infected drives into their systems. Others gain access to a system directly, then plug in a USB drive, and spread it through the network. Add to that the proliferation of USB devices and charging cables, and you can see why attacks of this type can be incredibly successful.
Let’s see an example. You are an employee working for a private company and you receive an Amazon package (with the official tape and everything you would expect from a legitimate parcel). You open it and find a sealed USB device. Thinking it’s brand new (maybe a gift from someone, you wonder), you plug it in. And then the chain reaction begins.
USB attacks can be highly targeted and tailored to steal sensitive data in a way that many people would not suspect. This is, in fact, what happened to Iran’s nuclear program in 2010 (Stuxnet), the Ukraine power grid in 2015 and 2016, and Sony Pictures Entertainment in 2014.
Types of USB Attacks and How They Work
Many attackers preload malware onto USB flash drives and scatter them in public places or send them directly to targeted individuals or organizations. Unsuspecting users insert these infected drives into their computers, unknowingly executing the malware (for example, a malicious DLL) and compromising their systems.
There are different types of USB threats, including various methods such as keystroke injection attacks like Rubber Ducky, malicious firmware reprogramming, and social engineering tactics like USB drop attacks. Let’s see each of these in a little more detail.
Keystroke Injection
This type of human interface device (HID) can interact directly with human users— via mice, game controllers, and other input devices—and exploit the ability of certain USB devices to emulate keyboards. Attackers preload these devices with scripts that execute specific commands upon insertion, allowing them to perform various malicious actions on the target system.
Firmware Reprogramming or BadUSB Attack
BadUSB attacks involve reprogramming the firmware of USB devices—such as keyboards, mice, or thumb drives—to emulate other devices or execute malware infection commands. Once plugged into a computer through a USB port, the compromised device can perform unauthorized actions, such as keystroke logging or spreading malware.
USB Drop Attack
In a USB drop attack, attackers leave infected USB devices in public spaces, hoping that unsuspecting individuals will pick them up and connect them to their computers. Once inserted, the USB dropper installs malware or initiates a phishing attack to initiate data transfer, provide remote access, or compromise the victim’s system.
Popular USB Drive Threats for 2024
We mentioned USB attacks were making a comeback. Here are three popular and recent USB drive threats that should give you some ideas of what to watch for in 2024:
- SOGU malware infection: This threat involves the use of USB flash drives to load the SOGU malware, allowing attackers to steal sensitive information from a host. It is attributed to TEMP.Hex, a China-linked cyber espionage actor targeting various industries across different geographies.
- SNOWYDRIVE malware infection: This threat targets oil and gas organizations in Asia by using USB flash drives to deliver the SNOWYDRIVE malware. Once loaded, this malware creates a backdoor on the host system, enabling remote control and propagation throughout the network. UNC4698 is attributed to this campaign.
- WispRider infection: WispRider is a malware variant that spreads quickly across networks through USB drives, even infecting air-gapped systems. This threat involves manipulating files on USB drives to infect machines when users click on malicious files masquerading as legitimate executables. Mustang Panda is associated with this USB-based attack vector.
How to Prevent USB Attacks
It is definitely possible to mitigate the risk of USB attacks. For example, some preventive measures include:
- Use endpoint security solutions: Implement endpoint security solutions that can detect and block malicious USB devices and activities.
- Educate users: Teach users about the risks of inserting unknown USB devices into their computers and encourage them to report suspicious findings.
- Disable AutoRun feature: Disable the AutoRun feature on computers to prevent the automatic execution of programs when USB devices are connected.
- Regularly update systems: Keep operating systems and security software up to date to patch known vulnerabilities that could be exploited by USB attacks.
- Use USB security tools: Utilize USB security tools that can analyze and block malicious USB activity, such as unauthorized file transfers or device emulation.
Preparing for What’s Next
While advancements in cybersecurity have mitigated some threats, USB attacks remain prevalent and pose significant risks to individuals and businesses alike. However, you can protect yourself from malicious payloads by implementing the appropriate security measures.
Coro is an industry-leading, modular, cybersecurity solution that provides robust enterprise-grade modules to help organizations defend against USB attacks and mitigate the associated risks.
Coro’s security platform includes advanced malware detection and prevention mechanisms specifically designed to identify malicious payloads delivered through various devices, as well as comprehensive endpoint protection solutions that safeguard endpoints from USB-based threats.
Contact us to learn more about our cybersecurity modules and how they easily snap together to create the perfect security strategy tailored to your organization.