There’s always a part of the security stack no one wants to touch.
Not because it’s working perfectly, but because no one is entirely sure what will happen if it changes.
Over time, environments pick up layers: tools, policies, integrations. Each one was added for a good reason. But the reasoning behind them doesn’t always stay visible.
What’s left is a system that functions, but depends on assumptions that are harder to trace than they should be.
The inheritance problem isn’t about tools. It’s about lost context.
This is what often shows up as the inheritance problem. Technology is brought in by intelligent people with great intentions. But, roles change. Team members or leadership move on. And with each transition, some context naturally goes with them: the reasoning behind a policy, the workaround supporting an integration, or simply which dashboard reflects what’s happening.
At some point, the next person inherits a system they didn’t build, along with documentation that may not tell the full story.
For lean IT teams managing multiple environments, that challenge compounds quickly. The issue is the growing operational burden of trying to maintain disconnected systems that don’t share context with each other.
Misconfiguration isn’t the cause. It’s the symptom.
Misconfiguration is often cited as the root cause behind breaches in mid-market and SMB environments. But misconfiguration is just what gets reported. Loss of context is what creates it.
The system is configured the way it is because no one currently responsible has a complete picture of why it was set up that way. The assumptions behind earlier decisions have drifted away from current reality, but the configurations remain.
What makes this harder is that most security tools only understand their own slice of the environment. Email sees email. Endpoint sees endpoint. Identity sees identity. The burden of connecting those signals – and determining what actually matters – still falls on people.
Fragmentation turns small risks into systemic ones
The pattern is familiar to anyone who has inherited an environment.
- A legacy email gateway no one wants to touch because the rule set has been modified by people who are no longer reachable.
- An endpoint agent tied to a licensing model no one fully understands.
- A cloud security tool everyone agrees is incomplete, but no one has the bandwidth to replace.
Each one is a small risk on its own. The aggregate is a security posture that nobody designed, and nobody fully owns. Not because the tools themselves are ineffective, but because they operate independently and without shared context. Each tool sees part of the environment, but nothing sees the whole.
What appears as separate alerts across email, endpoints, data, network, and cloud is often a single coordinated attack moving between them. And someone has to piece that together, manually.
That manual correlation work becomes increasingly difficult as environments scale. More tools create more consoles, more alerts, more handoffs, and more operational drag, especially for teams already wearing multiple hats.
Adding tools doesn’t fix fragmentation. It compounds it.
Each new product introduces its own console, its own policy logic, its own alerting model, and its own learning curve.
Instead of reducing risk, the system becomes harder to understand, harder to maintain, and more reliant on constant attention just to keep everything aligned.
Whoever inherits the environment next inherits an even larger system they need to make sense of.
Consolidation isn’t about fewer tools. It’s about a shared system.
The structural answer isn’t necessarily about reduction. It’s consolidation.
Not fewer tools for the sake of simplicity — but a unified system where policy, visibility, and response are shared across email, endpoints, data, network, and cloud.
That distinction matters. A true platform isn’t simply a collection of integrated point solutions. It’s a shared operating model where signals, policies, telemetry, and intelligence work together natively across the environment.
When security operates as a single system instead of a collection of independent tools, activity can be correlated across environments. Signals are connected. Context is preserved.
Instead of forcing someone to interpret disconnected alerts, the system helps surface what matters — and supports faster, more confident decisions.
That changes the nature of the work and the reliability of the outcome.
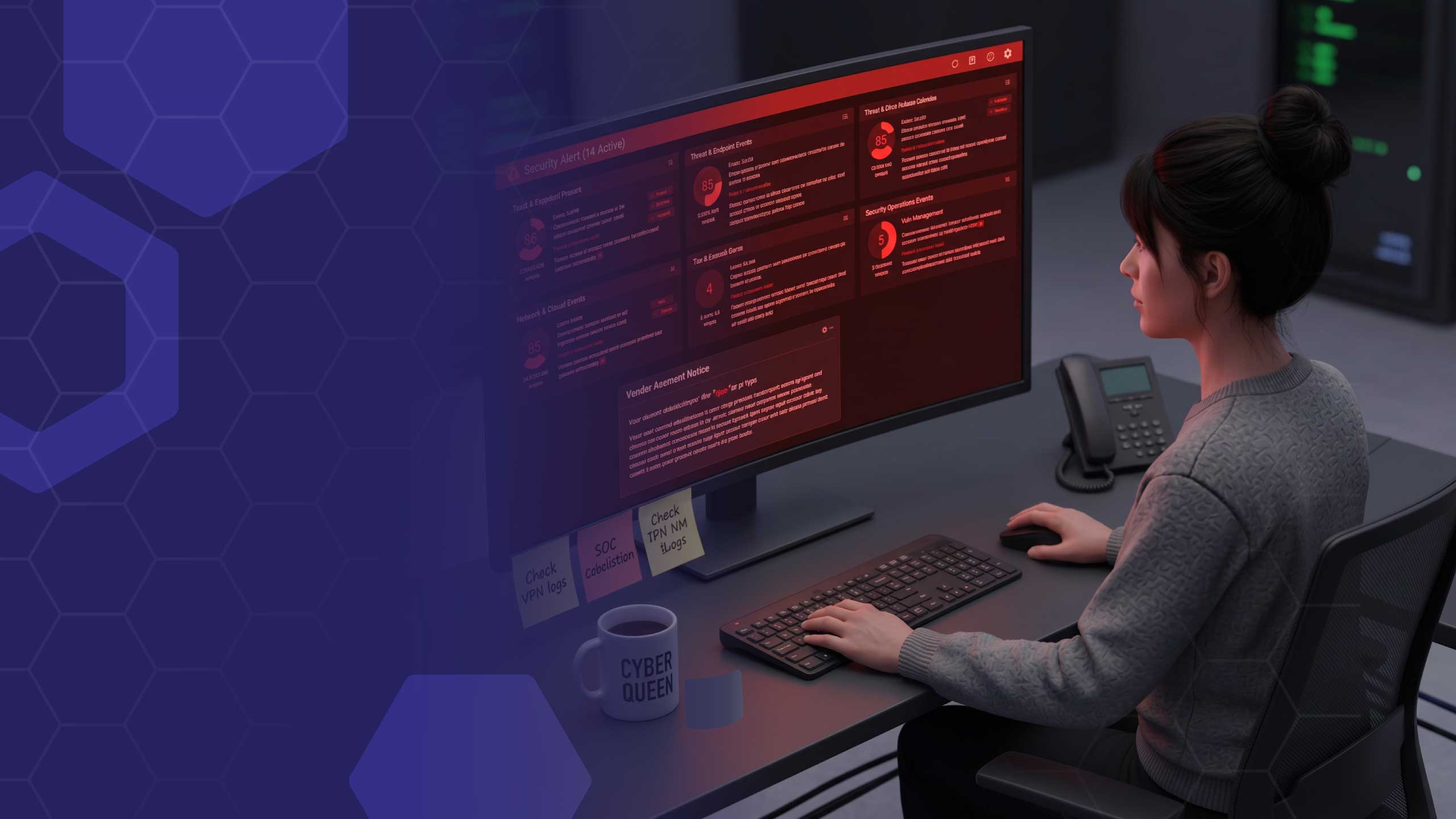
A unified system supports the people running it
Platform consolidation doesn’t remove the need for people; it changes what they spend their time on.
When policy is shared, visibility is unified, and activity is correlated across systems, the environment becomes easier to understand and manage.
That means:
- Less time piecing together fragmented signals
- More confidence acting on what’s actually happening
- More room to focus on priorities beyond constant triage
New team members can get oriented faster. Experienced team members can go deeper where it matters. Instead of relying on one person to hold everything together, the system helps make the work more accessible to the team as a whole.
Automation plays an important role here not by replacing human oversight, but by reducing repetitive manual work and helping teams focus attention where expert, human judgment matters most.
When AI operates across a unified platform instead of isolated tools, it gains the context needed to help prioritize activity, correlate signals, and reduce alert fatigue in ways fragmented environments cannot.
The result is better-supported teams that can operate more efficiently without losing visibility or control.
The goal is to design a system that supports everyone
An inherited stack is a record of decisions made by people who left, in conditions that may no longer apply. Trying to reconstruct that history isn’t a strategy.
Designing a system that makes it easier to understand, manage, and act (without needing to piece everything together manually) is.
Because the environments that scale best over time are the ones where the platform itself helps preserve context, reduce operational burden, and support the people responsible for protecting it.
If you inherited the stack, you don’t have to carry all of its complexity forward. See what changes when security operates through one unified platform with shared intelligence instead of disconnected tools competing for attention.
Read More about the Coro Unified Platform